Xerub has posted the decryption key for the security coprocessor was introduced alongside the iPhone 5s and Touch ID.
SEP performs secure services for the rest of the SOC and prevents the main processor from getting direct access to sensitive data. It runs its own operating system (SEPOS) which includes a kernel, drivers, services, and applications.
It processes fingerprint data from the Touch ID sensor and works out if there is a match against registered fingerprints, and then enabling access or purchases on behalf of the user. Communication between the processor and the Touch ID sensor takes place over a serial peripheral interface bus. The processor then forwards the data to the Secure Enclave but can't read it. It's encrypted and authenticated with a session key that is negotiated using the device's shared key that is provisioned for the Touch ID sensor and the Secure Enclave. The session key exchange uses AES key wrapping with both sides providing a random key that establishes the session key and uses AES-CCM transport encryption.
Using Xerub’s decryption key you can use img4lib to decrypt the firmware and xerub's SEP firmware split tool to process. This will make it easier for hackers and security researchers to comb through the SEP for vulnerabilities.
Published in
News
Hackers penetrate Apple's inner sanctum
Security coprocessor has been hacked
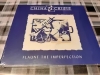
A hacker by name of "Xerub" has made a mockery of Apple’s Apple's Secure Enclave Processor (SEP) firmware.