According to the EFF, journalists and political activists critical of Kazakhstan’s authoritarian government, along with their family members, lawyers, and associates, started getting sent loads of online phishing and malware.
Once they opened the documents surveillance software capable of recording keystrokes, recording through the webcam were installed on their machine.
This was not exactly high tech - in fact anyone can buy this sort of software for $40 online. Curiously it was rather successful and might have helped Kazakhstan track down the wife and young daughter of one dissident who were legally hiding in Italy. The Kazakhstan government kicked up a stink and demanded that the Italians handed them over.
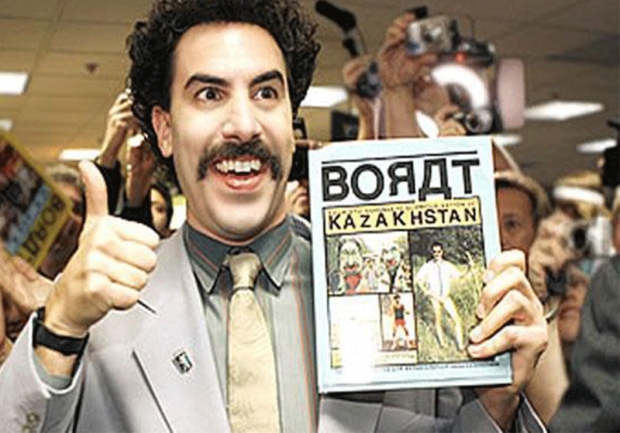
Other targets of the malware campaign are also involved in litigation with the government of Kazakhstan, including the publishers of Respublika.
Eva Galperin, Global Policy Analyst at EFF said that the use of malware to spy on and intimidate dissidents beyond their borders is an increasingly common tactic employed by oppressive governments.
EFF researchers found overlaps between Operation Manul and Appin Security Group, an Indian company that has been linked with several other attack campaigns.
EFF Staff Technologist Cooper Quintin said that Appin has been linked by cybersecurity firm Norman Shark to cyber-attacks against a Norwegian telecom company, Punjabi separatists, and others.
“We found that some of the technology infrastructure used in those cyber-attacks overlapped with the infrastructure used in Operation Manul. “
“Our research shows that such cheap, commercially available malware can have a real impact on vulnerable populations. Much of the past research in this area has exposed campaigns carried out by governments using spy software which they have purchased. In this case, the evidence suggests that the government of Kazakhstan hired a company to carry out the attacks on their behalf."